15 Reasons You Need ERP On The Salesforce Platform
Nothing is more important than the security of your data and applications. This is one reason why Rootstock chose the Salesforce Platform for our cloud ERP applications. The Salesforce Platform was built on the principles of trust and transparency and is certified by many standards and practices organizations (AICPA SOC1, SOC2 and SOC3, TRUSTe and more). Rootstock Software is also certified as SOC 1- and SOC 2-compliant. You can trust the combination of Rootstock Cloud ERP and the Salesforce Platform to keep your data safe with complete transparency to system performance and security information.
Rootstock Controls
Ensuring Data Integrity & Security
Today, manufacturers, distributors, and supply chain organizations collect, manage and analyze more data via ERP systems than ever before. These organizations leverage this data throughout their business, but they also want to ensure proper controls around this information. In striving to deliver a superior Cloud ERP solution, we at Rootstock Software have implemented sophisticated controls to safeguard our customer data.
Successful SOC 1 Type II and SOC 2 Type II Audit Examination
To attest to the quality of our controls, we completed a SOC 1 (SSAE 18) Type II and SOC 2 Type II audit examination, which validated our data security standards and operations, and demonstrated our commitment to the highest level of data integrity.
Moss Adams LLP, one of the largest public accounting firms in the United States, conducted the evaluation. Through this audit, it confirmed Rootstock had quality and suitable levels of controls and security in place for SOC 1 and 2 compliance:
- SOC 1 is based on AICPA Statement of Standards for Attestation Engagements (SSAE) 18 and evaluates the effect of controls on financial statement assertions. Moss Adams’ testing of Rootstock’s control environment included an examination of policies and procedures. As a result, Rootstock now has a SOC 1 Type II report confirming internal controls around financial reporting for the purposes of complying with laws and regulations.
- SOC 2 is based on the AICPA guide, Reporting on Controls at a Service Organization Relevant to Security, Availability, Processing Integrity, Confidentiality, or Privacy. Rootstock now has a SOC 2 Type II report confirming the suitability of the design and operating effectiveness of its internal controls. The audit evaluated key elements of security, availability, processing integrity, and confidentiality. Moss Adams also examined Rootstock’s policies and procedures regarding network connectivity, firewall configurations, systems development life cycle, computer operations, logical access, data transmission and other critical operational areas of business.
Bottom-line Benefits
Rootstock’s completion of this SOC audit is among the highest and most rigorous data integrity accomplishments that can be achieved. Successful completion of this examination illustrates Rootstock’s ongoing commitment to create and maintain data integrity in a secure operating environment for the benefit of confidential information.
Rootstock received a service auditor’s report demonstrating that our policies, procedures, and infrastructure are suitably designed and operate effectively to meet or exceed stringent SOC 1 and SOC 2 criteria.
With these business processes in place, customers can rest assured that we take data integrity and security seriously, and as a result, our customers can stay focused on their main priorities – namely growing their businesses and focusing on their customers.
Salesforce Platform Security
Salesforce Platform security is based on the latest best practices and security technologies. Salesforce works with you so that your users can do their jobs securely and data is exposed only to those users who act on it.
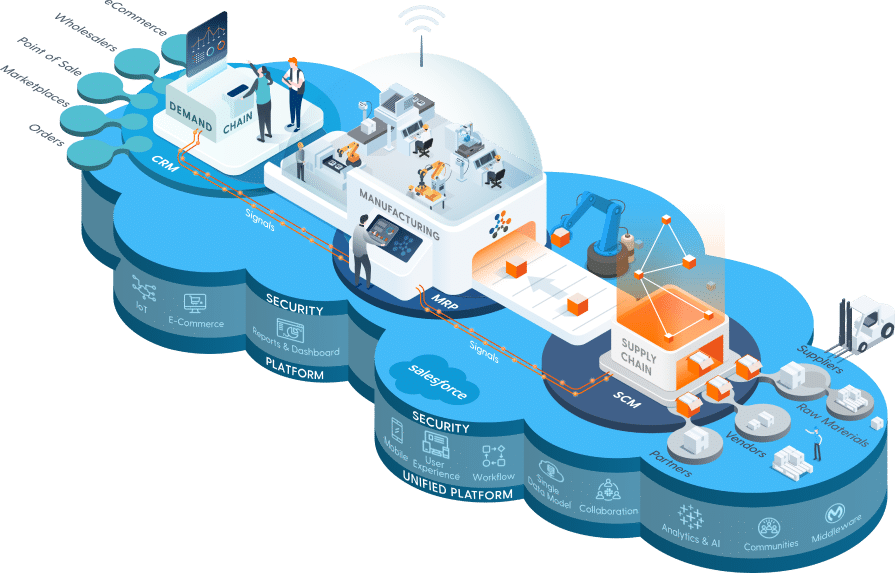
PROVEN, SECURE CLOUD PLATFORM
End-to-end control and visibility across the entire value chain.
How Does Salesforce Keep Your Data Safe?
Security functions are built into the Salesforce Platform:
- Salesforce Trust is a website and community hub that lets you view platform security status, including availability, privacy and compliance.
- Advanced event monitoring lets you receive detailed reports to help you quickly identify and resolve any suspicious activity, including phishing and malware.
- Two-factor authentication and identity verification ensures that only authorized users can access your data and applications.
- Organizational identifiers are assigned at the beginning of every new session to guarantee that data can only be accessed by the company that owns it.
- Transport Layer Security (TLS) encrypts your data to protect against attacks.
- Salesforce includes tools that identify security weaknesses introduced by users, such as passwords, network configurations and sessions settings.
- Auditing provides critical system usage information for diagnosing potential or real security issues. You run your own security audits to detect abuse, including record modifications, login histories, individual field tracking and setup audit trails, which log all changes to your system configuration.
- Transaction Security Policies let you evaluate activity with events. You can define real-time actions such as notify, block, force two-factor authentication, freeze user or end a session.
- Security Health Check lets you identify and fix potential vulnerabilities on a single screen.
- Salesforce Shield is a set of security tools that admins and developers can use to build trust, transparency, compliance and governance into their own custom business-critical apps. Salesforce Shield includes platform encryption, event monitoring, and field audit trails, which tell you the state and value of your data for any date and time.
Salesforce Security Resources
With Trust comes transparency. Salesforce provides numerous security resources online to help you learn more about platform security, system status, best practices and more.
| Resource | Description | Link |
| Salesforce Trust | Salesforce security online community hub. | https://trust.salesforce.com/ |
| Trust Status | View the service availability and performance of any Salesforce cloud platform. | https://status.salesforce.com/ |
| Stay Current on Security | Descriptions of security best practices recommended by Salesforce. | https://trust.salesforce.com/en/security/stay-current-security/ |
| Security for Administrators | Links to security information and resources for admins, including documentation, video and training. | https://trust.salesforce.com/en/security/for-administrators/ |
| Become a Security Trailblazer | Salesforce security self-training center. | https://trust.salesforce.com/security/security-resources |
| Resources for Developers | Links to security tools and resources for developers who build their own Salesforce apps. | https://trust.salesforce.com/en/security/for-developers/ |
| Security Developer Center | Resources to help developers learn how to build and secure Salesforce apps. | https://developer.salesforce.com/developer-centers/security/ |
| Trust Compliance | All Salesforce security certifications and compliance with standards and regulations. | https://compliance.salesforce.com/en |
IDW PS 880 Certification

IDW PS 880 Software Certification – Reliable Proof of the Compliance of Applications
The audit of software products by means of the auditing standard PS 880 of the Institute of Public Auditors in Germany (IDW) refers to the determination of compliance, independent of their implementation and going live. In this way, the software provider proves that its part of the responsibility within the framework of the fiscal obligations has been audited and confirmed as positive.
About Mazars
Mazars is a leading international firm specialized in audit, tax and advisory services. Mazars is your global partner for audit, tax and legal as well as accounting, financial advisory and consulting.
Our team in Germany consists of over 1,700 experts in 12 locations. We are the number eight leading audit and consulting firm in Germany. Understanding our clients and their environment forms the basis for our individual advisory approach and our tailor-made services.
With our broad geographical reach and our personal and agile approach, we are a strong partner for both global and local companies. Our clients include private individuals, medium-sized and family-run companies as well as international, regulated companies, but also start-ups and public organizations.
Our goal is always to create the economic foundations for a just and prosperous world by working for the success of our employees and clients, stable financial markets and the integrity of our industry.